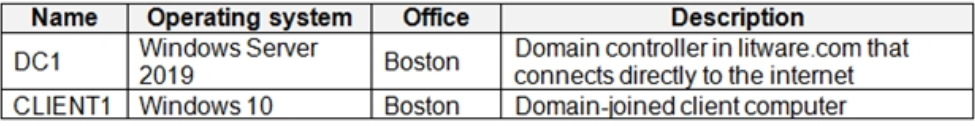
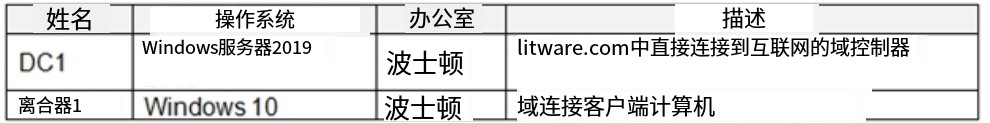
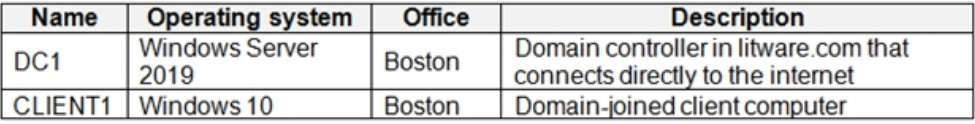
单选题 Overview - Litware Inc. is a renewable energy company. Litware has offices in Boston and Seattle. Litware also has remote users located across the United States. To access Litware resources, including cloud resources, the remote users establish a VPN connection to either office. Existing Environment - Identity Environment - The network contains an Active Directory forest named litware.com that syncs to an Azure Active Directory (Azure AD) tenant named litware.com. Microsoft 365 Environment - Litware has a Microsoft 365 E5 subscription linked to the litware.com Azure AD tenant. Microsoft Defender for Endpoint is deployed to all computers that run Windows 10. All Microsoft Cloud App Security built-in anomaly detection policies are enabled. Azure Environment - Litware has an Azure subscription linked to the litware.com Azure AD tenant. The subscription contains resources in the East US Azure region as shown in the following table. Network Environment - Each Litware office connects directly to the internet and has a site-to-site VPN connection to the virtual networks in the Azure subscription. On-premises Environment - The on-premises network contains the computers shown in the following table. Current problems - Cloud App Security frequently generates false positive alerts when users connect to both offices simultaneously. Planned Changes and Requirements Planned Changes - Litware plans to implement the following changes: Create and configure Azure Sentinel in the Azure subscription. Validate Azure Sentinel functionality by using Azure AD test user accounts. Business Requirements - Litware identifies the following business requirements: The principle of least privilege must be used whenever possible. Costs must be minimized, as long as all other requirements are met. Logs collected by Log Analytics must provide a full audit trail of user activities. All domain controllers must be protected by using Microsoft Defender for Identity. Azure Information Protection Requirements All files that have security labels and are stored on the Windows 10 computers must be available from the Azure Information Protection ג€" Data discovery dashboard. Microsoft Defender for Endpoint requirements All Cloud App Security unsanctioned apps must be blocked on the Windows 10 computers by using Microsoft Defender for Endpoint. Microsoft Cloud App Security requirements Cloud App Security must identify whether a user connection is anomalous based on tenant-level data. Azure Defender Requirements - All servers must send logs to the same Log Analytics workspace. Azure Sentinel Requirements - Litware must meet the following Azure Sentinel requirements: Integrate Azure Sentinel and Cloud App Security. Ensure that a user named admin1 can configure Azure Sentinel playbooks. Create an Azure Sentinel analytics rule based on a custom query. The rule must automatically initiate the execution of a playbook. Add notes to events that represent data access from a specific IP address to provide the ability to reference the IP address when navigating through an investigation graph while hunting. Create a test rule that generates alerts when inbound access to Microsoft Office 365 by the Azure AD test user accounts is detected. Alerts generated by the rule must be grouped into individual incidents, with one incident per test user account. You need to modify the anomaly detection policy settings to meet the Cloud App Security requirements and resolve the reported problem. Which policy should you modify?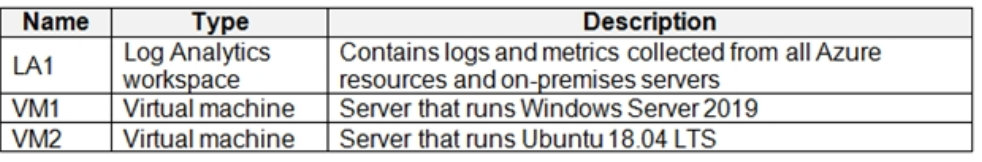
相关试题
单选题 概览- Litware公司是一家可再生能源公司。 Litware在波士顿和西雅图设有办事处。Litware也有位于美国各地的远程用户。要访问Litware资源,包括云资源,远程用户建立VPN连接到任一办公室。 现有环境- 身份识别环境-- 该网络包含一个名为litware.com的Active Directory林,该林同步到名为litware.com的AzureActiveDirectory(Azure AD)租户 微软365环境- Liware有一个微软365E5订阅链接到itware,.comAzureAD租户。Microsot Defenderfor Endpoint部署到运行Windows 10的所有计算机上。所有微软云应用安全内置异常检测策略都已启用。 Azure环境 Litware有一个Azure订阅链接到litware.com Azure AD租户。订阅包含下表所示的East US Azure区域中的资源。 网络环境一. 每个Litware办公室都直接连接到互联网,并通过站点到站点的VPN连接到Azure订阅中的虚拟网络。 内部环境- 本地网络包含下表所示的计算机。 目前存在的问题-当用户同时连接到两个办公室时,Cloud App Security经常会生成误报警报。计划变更和要求 计划中的变化-- Litware计划实施以下变化: 在Azure订阅中创建和配置Azure Sentinel. 使用Azure AD测试用户帐户验证Azure Sentinel功能。 业务需求- Litware确定了以下业务要求: 只要有可能,就必须使用最小特权原则 必须尽可能降低成本,只要满足所有其他要求。 由LogAnalytics收集的日志必须提供用户活动的完整审计跟踪。 所有域控制器都必须使用微软Defender forldentity进行保护。Azure信息保护要求存储在Windows 10计算机上的所有带有安全标签的文件必须可从Azure信息保护中使用。““数据发现仪表板。 Microsoft Defender for Endpoint需求 所有云应用程序安全未经批准的应用程序必须通过使用Microsoft Defender for Endpoint在Windows 10计算机上被阳止。微软云应用安全需求Cloud App Security必须根据租户级别的数据识别用户连接是否异常。 Azure Defender的需求 所有服务器都必须将日志发送到相同的日志分析工作区。 Azure Sentinel的要求一 Litware必须满足以下Azure Sentinel要求: 集成Azure Sentinel和云应用程序安全性。 确保名为admin1的用户可以配置Azure Sentinel剧本。 基于自定义查询创建Azure Sentinel分析规则。规则必须自动启动剧本的执行。向表示来自特定IP地址的数据访问的事件添加注释,以便在搜索时在调查图中导航时能够引用该IP地址。 创建测试规则,在检测到AzureAD测试用户帐户对Microsoft Office365的入站访问时生成警报。规则生成的警报必须分组为单个事件,每个测试用户帐户有一个事件。 您需要实现Azure信息保护要求。你应该先配置什么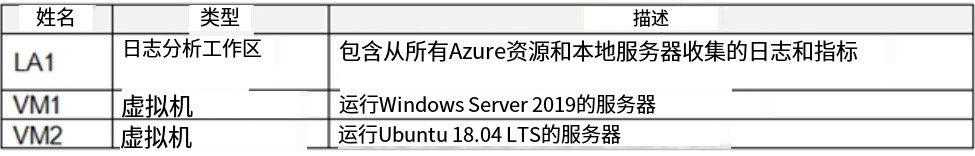
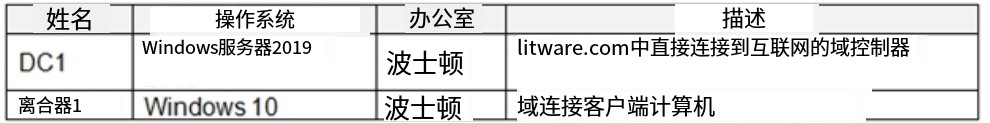
单选题 概览- Litware公司是一家可再生能源公司。 Litware在波士顿和西雅图设有办事处。Litware也有位于美国各地的远程用户。要访问Litware资源,包括云资源,远程用户建立VPN连接到任一办公室。 现有环境- 身份识别环境-- 该网络包含一个名为litware.com的Active Directory林,该林同步到名为litware.com的AzureActiveDirectory(Azure AD)租户 微软365环境- Liware有一个微软365E5订阅链接到itware,.comAzureAD租户。Microsot Defenderfor Endpoint部署到运行Windows 10的所有计算机上。所有微软云应用安全内置异常检测策略都已启用。 Azure环境 Litware有一个Azure订阅链接到litware.com Azure AD租户。订阅包含下表所示的East US Azure区域中的资源。 网络环境一. 每个Litware办公室都直接连接到互联网,并通过站点到站点的VPN连接到Azure订阅中的虚拟网络。 内部环境- 本地网络包含下表所示的计算机。 目前存在的问题-当用户同时连接到两个办公室时,Cloud App Security经常会生成误报警报。计划变更和要求 计划中的变化-- Litware计划实施以下变化: 在Azure订阅中创建和配置Azure Sentinel. 使用Azure AD测试用户帐户验证Azure Sentinel功能。 业务需求- Litware确定了以下业务要求: 只要有可能,就必须使用最小特权原则 必须尽可能降低成本,只要满足所有其他要求。 由LogAnalytics收集的日志必须提供用户活动的完整审计跟踪。 所有域控制器都必须使用微软Defender forldentity进行保护。Azure信息保护要求存储在Windows 10计算机上的所有带有安全标签的文件必须可从Azure信息保护中使用。““数据发现仪表板。 Microsoft Defender for Endpoint需求 所有云应用程序安全未经批准的应用程序必须通过使用Microsoft Defender for Endpoint在Windows 10计算机上被阳止。微软云应用安全需求Cloud App Security必须根据租户级别的数据识别用户连接是否异常。 Azure Defender的需求 所有服务器都必须将日志发送到相同的日志分析工作区。 Azure Sentinel的要求一 Litware必须满足以下Azure Sentinel要求: 集成Azure Sentinel和云应用程序安全性。 确保名为admin1的用户可以配置Azure Sentinel剧本。 基于自定义查询创建Azure Sentinel分析规则。规则必须自动启动剧本的执行。向表示来自特定IP地址的数据访问的事件添加注释,以便在搜索时在调查图中导航时能够引用该IP地址。 创建测试规则,在检测到AzureAD测试用户帐户对Microsoft Office365的入站访问时生成警报。规则生成的警报必须分组为单个事件,每个测试用户帐户有一个事件。 您需要修改异常检测策略设置,以满足Cloud App Security要求并解决报告的问题。您应该修改哪个策略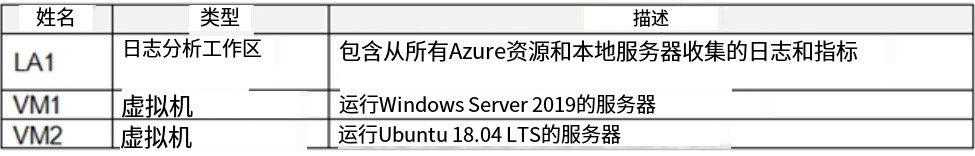
单选题 You need to receive a security alert when a user attempts to sign in from a location that was never used by the other users in your organization to sign in. Which anomaly detection policy should you use? 当用户尝试从组织中的其他用户从未使用过的位置登录时,您需要收到安全警报。您应该使用哪种异常检测策略?
单选题 Overview - Litware Inc. is a renewable energy company. Litware has offices in Boston and Seattle. Litware also has remote users located across the United States. To access Litware resources, including cloud resources, the remote users establish a VPN connection to either office. Existing Environment - Identity Environment - The network contains an Active Directory forest named litware.com that syncs to an Azure Active Directory (Azure AD) tenant named litware.com. Microsoft 365 Environment - Litware has a Microsoft 365 E5 subscription linked to the litware.com Azure AD tenant. Microsoft Defender for Endpoint is deployed to all computers that run Windows 10. All Microsoft Cloud App Security built-in anomaly detection policies are enabled. Azure Environment - Litware has an Azure subscription linked to the litware.com Azure AD tenant. The subscription contains resources in the East US Azure region as shown in the following table. Network Environment - Each Litware office connects directly to the internet and has a site-to-site VPN connection to the virtual networks in the Azure subscription. On-premises Environment - The on-premises network contains the computers shown in the following table. Current problems - Cloud App Security frequently generates false positive alerts when users connect to both offices simultaneously. Planned Changes and Requirements Planned Changes - Litware plans to implement the following changes: Create and configure Azure Sentinel in the Azure subscription. Validate Azure Sentinel functionality by using Azure AD test user accounts. Business Requirements - Litware identifies the following business requirements: The principle of least privilege must be used whenever possible. Costs must be minimized, as long as all other requirements are met. Logs collected by Log Analytics must provide a full audit trail of user activities. All domain controllers must be protected by using Microsoft Defender for Identity. Azure Information Protection Requirements All files that have security labels and are stored on the Windows 10 computers must be available from the Azure Information Protection ג€" Data discovery dashboard. Microsoft Defender for Endpoint requirements All Cloud App Security unsanctioned apps must be blocked on the Windows 10 computers by using Microsoft Defender for Endpoint. Microsoft Cloud App Security requirements Cloud App Security must identify whether a user connection is anomalous based on tenant-level data. Azure Defender Requirements - All servers must send logs to the same Log Analytics workspace. Azure Sentinel Requirements - Litware must meet the following Azure Sentinel requirements: Integrate Azure Sentinel and Cloud App Security. Ensure that a user named admin1 can configure Azure Sentinel playbooks. Create an Azure Sentinel analytics rule based on a custom query. The rule must automatically initiate the execution of a playbook. Add notes to events that represent data access from a specific IP address to provide the ability to reference the IP address when navigating through an investigation graph while hunting. Create a test rule that generates alerts when inbound access to Microsoft Office 365 by the Azure AD test user accounts is detected. Alerts generated by the rule must be grouped into individual incidents, with one incident per test user account. You need to implement the Azure Information Protection requirements. What should you configure first?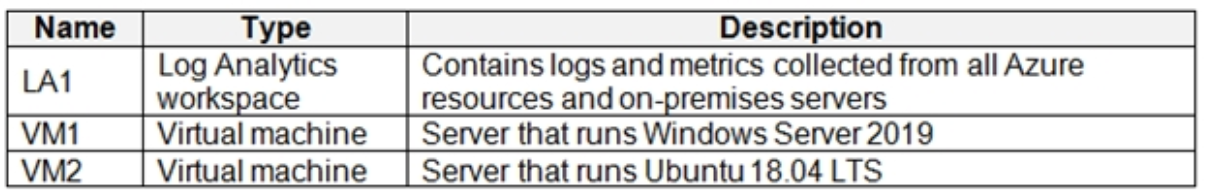
单选题 Overview - A company named Contoso Ltd. has a main office and five branch offices located throughout North America. The main office is in Seattle. The branch offices are in Toronto, Miami, Houston, Los Angeles, and Vancouver. Contoso has a subsidiary named Fabrikam, Ltd. that has offices in New York and San Francisco. Existing Environment - End-User Environment - All users at Contoso use Windows 10 devices. Each user is licensed for Microsoft 365. In addition, iOS devices are distributed to the members of the sales team at Contoso. Cloud and Hybrid Infrastructure - All Contoso applications are deployed to Azure. You enable Microsoft Cloud App Security. Contoso and Fabrikam have different Azure Active Directory (Azure AD) tenants. Fabrikam recently purchased an Azure subscription and enabled Azure Defender for all supported resource types. Current Problems - The security team at Contoso receives a large number of cybersecurity alerts. The security team spends too much time identifying which cybersecurity alerts are legitimate threats, and which are not. The Contoso sales team uses only iOS devices. The sales team members exchange files with customers by using a variety of third-party tools. In the past, the sales team experienced phishing attacks on their devices. The marketing team at Contoso has several Microsoft SharePoint Online sites for collaborating with external vendors. The marketing team has had several incidents in which vendors uploaded files that contain malware. The executive team at Contoso suspects a security breach. The executive team requests that you identify which files had more than five activities during the past 48 hours, including data access, download, or deletion for Microsoft Cloud App Security-protected applications. Requirements - Planned Changes - Contoso plans to integrate the security operations of both companies and manage all security operations centrally. Technical Requirements - Contoso identifies the following technical requirements: Receive alerts if an Azure virtual machine is under brute force attack. Use Azure Sentinel to reduce organizational risk by rapidly remediating active attacks on the environment. Implement Azure Sentinel queries that correlate data across the Azure AD tenants of Contoso and Fabrikam. Develop a procedure to remediate Azure Defender for Key Vault alerts for Fabrikam in case of external attackers and a potential compromise of its own Azure AD applications. Identify all cases of users who failed to sign in to an Azure resource for the first time from a given country. A junior security administrator provides you with the following incomplete query. BehaviorAnalytics - | where ActivityType == "FailedLogOn" | where ________ == True The issue for which team can be resolved by using Microsoft Defender for Endpoint?
单选题 概览: 一家名为Contoso有限公司的公司在北美有一个总办事处和五个分办事处。主要办公室在西雅图。分公司位于多伦多、迈阿密、休斯顿、洛杉矶和温哥华。Contoso在纽约和旧金山设有办事处的子公司Fabrikam,Ltd。 现有环境- 最终用户环境-Contoso的所有用户都使用Windows10设备。每个用户都有微软365的授权。此外,iOS的设备被分配给Contoso的销售团队的成员。 云和混合基础设施一所有Contoso应用程序都部署到Azure。 您启用微软云应用程序安全性。 contoso和Fabrikam拥有不同的Azure Active Directory(AzureAD)租户。Fabrikam最近购买了Azure订阅,并为所有受支持的资源类型启用了Azure Defender。 目前存在的问题一 Contoso的安全团队收到大量网络安全警报。安全团队花费了太多的时间来确定哪些网络安全警报是合法的威物,哪些不是,康多索的销售团队只使用iOS的设备。销售团队成员通过使用各种第三方工具与客户交换文件。在过去,销售团队经历过网络钓鱼攻击在他们的设备上。 Contoso的营销团队有几个微软sharePoint online网站,用于与外部供应商合作。营销团队曾发生过几起供应商上传包含恶意软件的文件的事件。Contoso的管理团队怀疑有安全漏洞。执行团队要求您确定哪些文件在过去48小时内有超过5个活动,包括Microsoft cloudApp安全保护应用程序的数据访问、下载或删除。 所需资源- 计划中的变化一 Contoso计划整合两家公司的安全运营,并集中管理所有的安全运营。 技术要求-- Contoso确定了以下技术要求: 如果Azure虚拟机受到暴力攻击,则接收警报。使用Azure Sentinel快速修复对环境的主动攻击,从而降低组织风险。实现Azure Sentinel查询,将Contoso和Fabrikam的Azure AD租户之间的数据关联起来。制定针对Fabrikam的密钥保管库警报的Azure Defender补救程序,以防外部攻击者及其自身Azure受到潜在威胁 AD的应用程序。 识别从给定国家/地区首次登录Azure资源失败的用户的所有情况。初级安全管理员为您提供了以下不完整的查询。 BehaviorAnalytics - | where ActivityType == "FailedLogOn" | where ________ == True The issue for which team can be resolved by using Microsoft Defender for Endpoint?
单选题 概览: 一家名为Contoso有限公司的公司在北美有一个总办事处和五个分办事处。主要办公室在西雅图。分公司位于多伦多、迈阿密、休斯顿、洛杉矶和温哥华。Contoso在纽约和旧金山设有办事处的子公司Fabrikam,Ltd。 现有环境- 最终用户环境-Contoso的所有用户都使用Windows10设备。每个用户都有微软365的授权。此外,iOS的设备被分配给Contoso的销售团队的成员。 云和混合基础设施一所有Contoso应用程序都部署到Azure。 您启用微软云应用程序安全性。 contoso和Fabrikam拥有不同的Azure Active Directory(AzureAD)租户。Fabrikam最近购买了Azure订阅,并为所有受支持的资源类型启用了Azure Defender。 目前存在的问题一 Contoso的安全团队收到大量网络安全警报。安全团队花费了太多的时间来确定哪些网络安全警报是合法的威物,哪些不是,康多索的销售团队只使用iOS的设备。销售团队成员通过使用各种第三方工具与客户交换文件。在过去,销售团队经历过网络钓鱼攻击在他们的设备上。 Contoso的营销团队有几个微软sharePoint online网站,用于与外部供应商合作。营销团队曾发生过几起供应商上传包含恶意软件的文件的事件。Contoso的管理团队怀疑有安全漏洞。执行团队要求您确定哪些文件在过去48小时内有超过5个活动,包括Microsoft cloudApp安全保护应用程序的数据访问、下载或删除。 所需资源- 计划中的变化一 Contoso计划整合两家公司的安全运营,并集中管理所有的安全运营。 技术要求-- Contoso确定了以下技术要求: 如果Azure虚拟机受到暴力攻击,则接收警报。使用Azure Sentinel快速修复对环境的主动攻击,从而降低组织风险。实现Azure Sentinel查询,将Contoso和Fabrikam的Azure AD租户之间的数据关联起来。制定针对Fabrikam的密钥保管库警报的Azure Defender补救程序,以防外部攻击者及其自身Azure受到潜在威胁 AD的应用程序。 识别从给定国家/地区首次登录Azure资源失败的用户的所有情况。初级安全管理员为您提供了以下不完整的查询。 BehaviorAnalytics - | where ActivityType == "FailedLogOn" | where ________ == True The issue for which team can be resolved by using Microsoft Defender for Office365?
单选题 Overview - A company named Contoso Ltd. has a main office and five branch offices located throughout North America. The main office is in Seattle. The branch offices are in Toronto, Miami, Houston, Los Angeles, and Vancouver. Contoso has a subsidiary named Fabrikam, Ltd. that has offices in New York and San Francisco. Existing Environment - End-User Environment - All users at Contoso use Windows 10 devices. Each user is licensed for Microsoft 365. In addition, iOS devices are distributed to the members of the sales team at Contoso. Cloud and Hybrid Infrastructure - All Contoso applications are deployed to Azure. You enable Microsoft Cloud App Security. Contoso and Fabrikam have different Azure Active Directory (Azure AD) tenants. Fabrikam recently purchased an Azure subscription and enabled Azure Defender for all supported resource types. Current Problems - The security team at Contoso receives a large number of cybersecurity alerts. The security team spends too much time identifying which cybersecurity alerts are legitimate threats, and which are not. The Contoso sales team uses only iOS devices. The sales team members exchange files with customers by using a variety of third-party tools. In the past, the sales team experienced phishing attacks on their devices. The marketing team at Contoso has several Microsoft SharePoint Online sites for collaborating with external vendors. The marketing team has had several incidents in which vendors uploaded files that contain malware. The executive team at Contoso suspects a security breach. The executive team requests that you identify which files had more than five activities during the past 48 hours, including data access, download, or deletion for Microsoft Cloud App Security-protected applications. Requirements - Planned Changes - Contoso plans to integrate the security operations of both companies and manage all security operations centrally. Technical Requirements - Contoso identifies the following technical requirements: Receive alerts if an Azure virtual machine is under brute force attack. Use Azure Sentinel to reduce organizational risk by rapidly remediating active attacks on the environment. Implement Azure Sentinel queries that correlate data across the Azure AD tenants of Contoso and Fabrikam. Develop a procedure to remediate Azure Defender for Key Vault alerts for Fabrikam in case of external attackers and a potential compromise of its own Azure AD applications. Identify all cases of users who failed to sign in to an Azure resource for the first time from a given country. A junior security administrator provides you with the following incomplete query. BehaviorAnalytics - | where ActivityType == "FailedLogOn" | where ________ == True The issue for which team can be resolved by using Microsoft Defender for Office 365?

 2024-04-10
2024-04-10
 共85道
共85道
